PureKit: Data at Rest Security
Security framework for user passwords and data protection in a database
with functionality against online and offline attacks
Virgil PureKit features
Choose your own use case to protect sensitive data at rest.
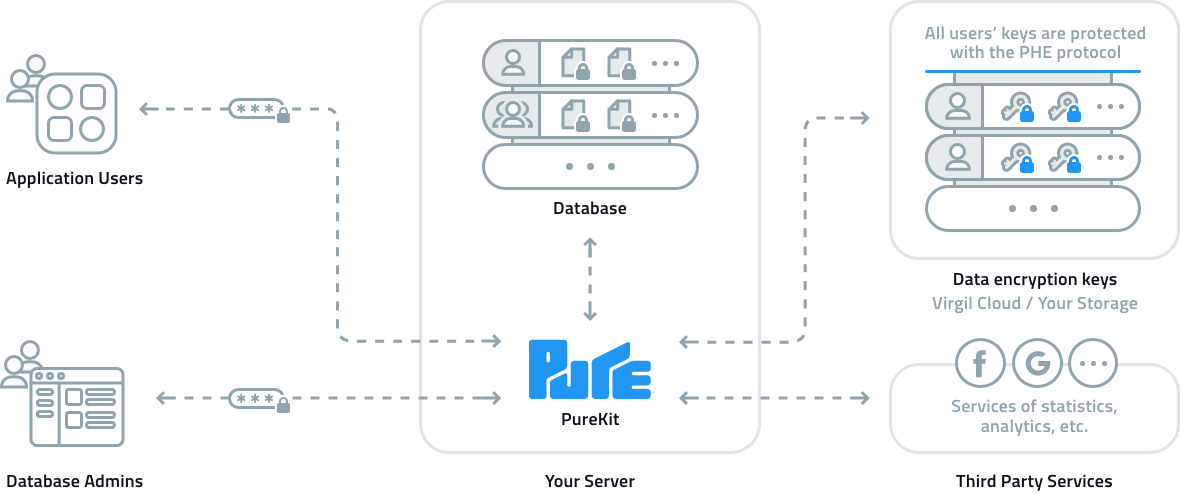
How it works
Data access control based on per-user encryption key management. Learn more
Benefits
At least 6 reasons to choose Virgil PureKit for data encryption at rest.
- 1
End-users control their data and encryption keys
Data can only be decrypted with a user’s personal encryption key, which itself is only available for the user who knows the password. - 2
More secure than AWS and Google key management systems
Unlike others, PureKit provides user-specific encryption and a solution for protecting data beyond the inevitable database compromisation. - 3
Stronger than encryption at-rest and TDE
PureKit provides data encryption with a number of advantages compared to TDE and encryption at-rest, such as more efficient keys infrastructure, PCS, and more. - 4
Provides protection against SQL injection
PureKit is immune to SQL injection because the data is not stored as plaintext. - 5
Encryption occurs regardless of database security
PureKit provides end-to-end encryption; therefore, data security does not rely on any device, network, or cloud provider. - 6
Post-compromise security for stored data
PureKit allows instantly invalidate stolen databases by rotating keys and records remotely.
Comply with Acts and Laws
Virgil Security builds developer toolkits that solve business problems by encrypting data and therefore lessening legal and compliance liability.
PCI DSS
Payment Card Industry Data Security Standard
CCPA
California Consumer Privacy Act
GDPR
General Data Protection Regulation
HIPAA
Health Insurance Portability and Accountability Act
From developers
for developers
We provide cross-platform, transparent and easy-to-use libraries. Here are some code snippets from our PureKit.
Explore documentation// Register a user and encrypt their password
pure.registerUser("alice", "VeryStrongPassword");
// Authenticate the user and verify their password
AuthResult authResult = pure.authenticateUser("alice", "VeryStrongPassword");
// Encrypt the user’s SSN (Social Security Number) with their personal key
byte[] cipherText = pure.encrypt("alice", "SSN", "AAA-GG-SSSS");
// Decrypt the encrypted user’s SSN after the user has been authenticated
byte[] plainText = pure.decrypt(authResult.getGrant(), "SSN", cipherText);
Blog highlights
Get started now with our easy-to-follow guides.
Start free, pay $0.02/month per user beyond 250 users.
Use cases across all industries
Healthcare
Make your communication platform and backend HIPAA-compliant.
Financial
Manage cardholder data and personal financial information within a PCI DSS-compliant system.
Automotive
Build IEEE-1609.2-compliant security solutions for protecting V2X communication.
Cloud
Protect and manage access to sensitive data in the сloud storage.
Internet of Things
Secure IoT devices from manufacturing to the end-user experience.
Industry 4.0
Build a fully protected industrial ecosystem and securely manage it across the stack.